Issue 8 Hacks, Leaks, and Breaches »

Issue 8 Hacks, Leaks, and Breaches »


Issue 8 Hacks, Leaks, and Breaches »
Issue 9 Little Development Devices / Humanitarian Goods »

Issue 8 Hacks, Leaks, and Breaches »

Issue 8 Hacks, Leaks, and Breaches »

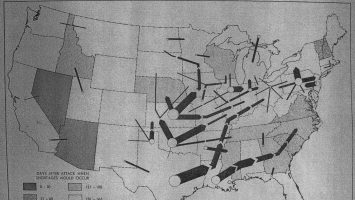
Issue 7 Public Infrastructures/Infrastructural Publics »

Issue 9 Little Development Devices / Humanitarian Goods »


Issue 9 Little Development Devices / Humanitarian Goods »

Issue 8 Hacks, Leaks, and Breaches »

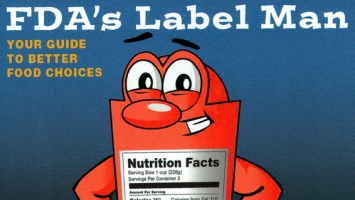
Issue 4 Food Infrastructures »
Issue 8 Hacks, Leaks, and Breaches »

Issue 7 Public Infrastructures/Infrastructural Publics »

Issue 7 Public Infrastructures/Infrastructural Publics »

Issue 8 Hacks, Leaks, and Breaches »
Issue 4 Food Infrastructures »
Issue 7 Public Infrastructures/Infrastructural Publics »

Limn finally has a new website! Please check it out: explore all our issues, our new list of Limn researchers, and take a look at our new downloadable PDFs of Limn’s print mag!
Issue 9 Little Development Devices / Humanitarian Goods »
Issue 8 Hacks, Leaks, and Breaches »

Issue 0 Prototyping Prototyping »
Issue 8 Hacks, Leaks, and Breaches »