Issue 8 Hacks, Leaks, and Breaches »

Issue 8 Hacks, Leaks, and Breaches »

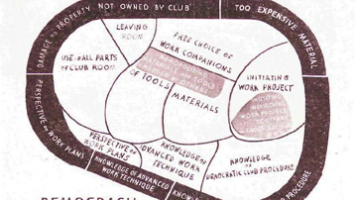
Issue 9 Little Development Devices / Humanitarian Goods »

Issue 8 Hacks, Leaks, and Breaches »
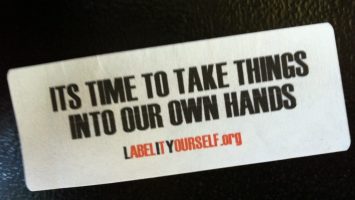
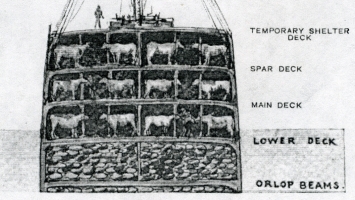
Issue 4 Food Infrastructures »
Issue 4 Food Infrastructures »

Issue 4 Food Infrastructures »
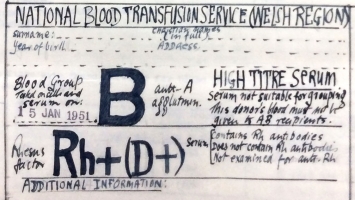
Issue 7 Public Infrastructures/Infrastructural Publics »
Issue 4 Food Infrastructures »
Issue 8 Hacks, Leaks, and Breaches »
Issue 8 Hacks, Leaks, and Breaches »

Issue 8 Hacks, Leaks, and Breaches »
Issue 8 Hacks, Leaks, and Breaches »
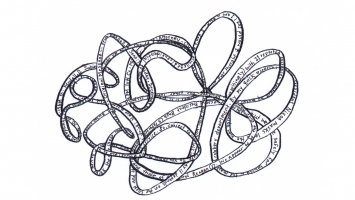
Issue 7 Public Infrastructures/Infrastructural Publics »

Issue 7 Public Infrastructures/Infrastructural Publics »



Issue 7 Public Infrastructures/Infrastructural Publics »

Issue 0 Prototyping Prototyping »

Issue 7 Public Infrastructures/Infrastructural Publics »

Issue 4 Food Infrastructures »
Issue 8 Hacks, Leaks, and Breaches »


Issue 8 Hacks, Leaks, and Breaches »
